Importance of Cybersecurity Technology in Hospitals
Hospitals, too, are ultimately nothing more than structures with complex building technology. It is constantly facing new threats, such as blackmail from the Internet. Thus, make cybersecurity as critical as having a hospital guard in the facility.
When the newspapers reported on 10 September 2020 of a failure of the IT systems at the University Hospital Düsseldorf (UKD), those responsible assumed a minor glitch that would be quickly remedied. A week later, it was clear that the problem was bigger. The number of affected patients grew steadily, some of which had been booked for months and had to be canceled. Instead of up to 120 operations a day, only 10 to 15 could be performed, and new patients were no longer admitted.
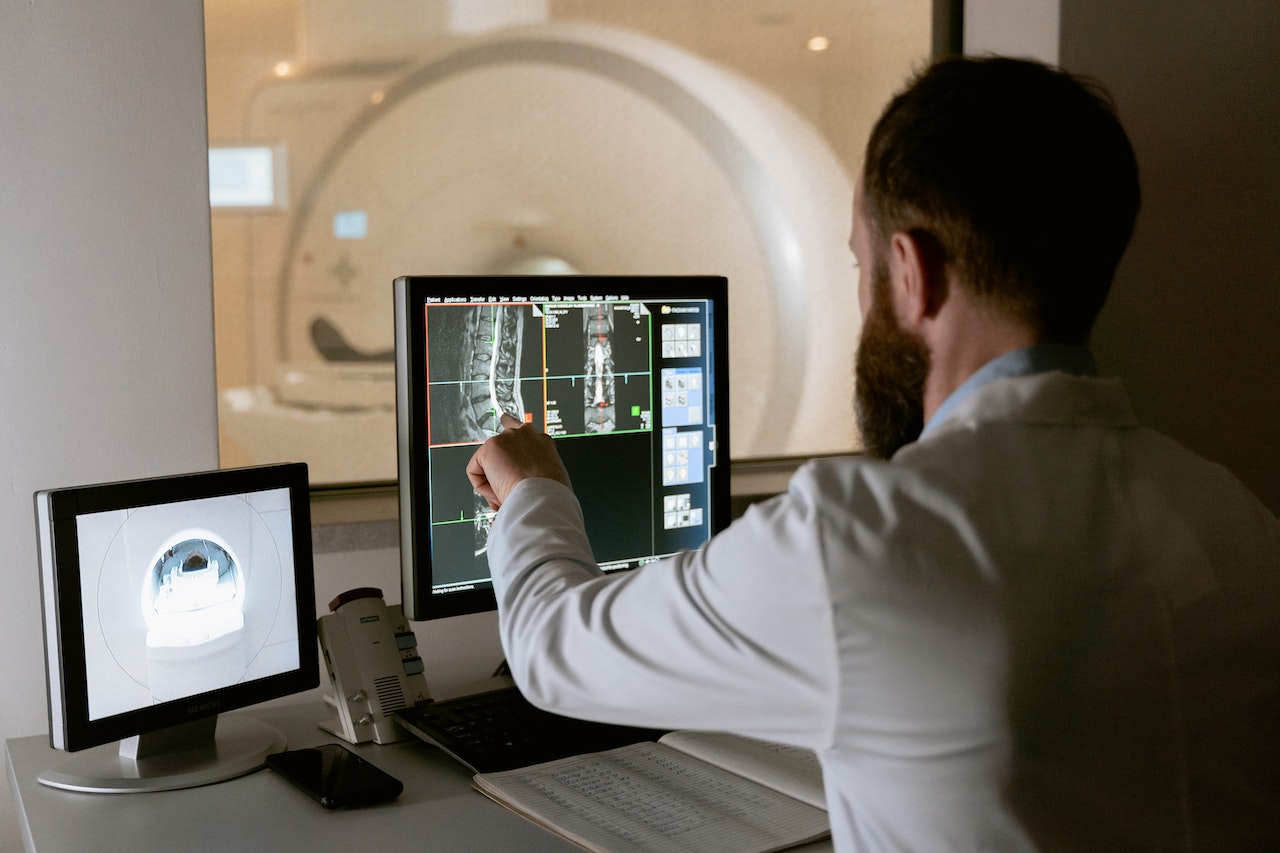
Although individual devices such as X-rays worked, the data obtained could not be fed into the UKD network. Apparently, the clinic had been the victim of a hacker attack, and accidentally. Because at the same time as the failures in the UKD, an extortion letter was received at the University of Düsseldorf. After being alerted to the crippled hospital, they sent a decryption key.
Regular attacks
For years, there have been regular attacks on authorities, universities, and research institutions. For the first time, this type of digital crime attracted public attention when all IT systems had to be shut down in February 2016 after a cyber attack at the Lukaskrankenhaus in Neuss. The hospital was only one destination among several. In addition, hospital computers in Mönchengladbach, Essen and Cologne, later also in Arnsberg were affected.
Thus, a new blackmail method had arrived in Germany, which was previously only known from US crime novels. Perpetrators usually use infected e-mail attachments to smuggle viruses onto computer systems that block access to systems and files or encrypt entire hard drives. With the help of this ransomware, criminals usually demand money to unlock the infected computer or decrypt the files.
Rebooting systems according to the prioritization list
After four days, the IT specialists in Neuss announced that the systems were virus-free. The next day, the successful restart of the systems could be started. In close coordination with the medical service areas, the Kristenstab decided on the following order: laboratory, SAP, radiotherapy, and in the end other areas.
First, the laboratory technology was ramped up because it forms the heart of the diagnostic and therapeutic process based on it. It makes a big difference whether a ward doctor waits an hour in the digital world for a requested laboratory result or a whole day in manual operation. Therefore, it was important to reconnect the laboratory to the systems first.
In second place was the SAP system to ensure the supply of hospital operations with required medicines and medical devices. After five days after the crisis, the clinic threatened to run out of drug stocks gradually. Ordering medicines, especially in quantities required by hospitals, is now an exclusively web-based process. In third place was the large radiotherapy with state-of-the-art linear accelerator technology.
Cancer patients may interrupt their radiation for a maximum of one week, otherwise, there is a risk of significant impairment of the quality of treatment. Otherwise, the doctors would have had to transfer about 100 patients to other facilities, which would have been associated with significant disadvantages for them as well as for the Lukas Hospital.
Widespread problem
As a rule, hospitals are reluctant to hang such events on the big bell, the concern about reputational damage is too great. The problem is much more widespread than is known to the public. For the “Hospital Study 2017” by the management consultancy Roland Berger, 64 percent of 500 hospitals surveyed stated that they had already been the victim of a hacker attack. The actual numbers are likely to be much higher, like any IT infrastructure, hospitals are the daily target of virtual attacks. As long as the defense systems are up to date, this is not a problem. Krämer also advises all responsible hospital managers to take out cyber insurance.
This would not protect against attacks, but it could help to cover the immense damage. With a probability of occurrence of over 50 percent, it is incomprehensible that significantly less than half of the companies have such insurance. Even four years after the events in Neuss, the problem is still topical. In August 2020, Interpol warned of increased cyber attacks on organizations in the health sector.
Actually quite astonishing, as several hacker groups had promised at the beginning of the corona pandemic not to attack hospitals. In fact, the opposite was the case, the antivirus specialist Bitdefender points out in its telemetry for the spring of 2020 a significant increase in targeted attacks on healthcare. Compared to the previous record, attacks on hospitals increased again by 73 percent in February, March and April. From February to March alone, the attack rate increased by 60 percent.
ALSO READ: Technologies That Changed The Coffee Machine
Defensive measures – safety before functionality
Of course, the most comprehensive possible protection against external attacks also plays an important role internally. Wherever people’s life and limb can be impaired, the principle of “safety before functionality” applies. For this purpose, the infrastructure at the Lukaskrankenhaus in Neuss was expanded to include two firewalls, a mail gateway, a NAC solution, and monitoring software.
In concrete terms, this meant strongly segmenting the network of the clinic, which has 600 to 700 end devices. This breakdown was carried out thematically according to departments, functions, or areas of responsibility. For example, medical technology, accounting, and administration each work in their own network.
Currently, the endpoints in the network consist of 50 percent fat clients and 50 percent thin clients from Igel. However, the IT department strives to implement as many thin clients as possible to minimize the number of attack vectors. They do not obtain their data and resources locally, but via the network, so they are only equipped with the bare necessities. In most cases, they are only used to display data and enter data. In contrast to full-featured fat clients, they offer a much lower vulnerability and risk of failure, for example by visiting a website with intentionally malicious code or a carelessly opened attachment to an e-mail.
Security by updating
One of the most important tools in defending against cyber attacks is to keep the equipment and the required software up to date. And this can sometimes lead to problems with legal requirements. The Medical Devices Act provides for full certification for devices used in the medical environment. This also applies to the software installed on it. Therefore, it is not possible to simply install current patches. Instead, the responsible employees have to wait for the certification of the new components.
This leads – if at all – to very long update cycles. Therefore, a number of systems at Lukaskrankenhaus still work with old Windows versions. They need to be separated from the other components on the network to make them less vulnerable. One device even runs a venerable, English Windows XP version without Service Pack 3. But ancient technology also has its advantages, with such old devices it is quite difficult to get into the network at all.
And what is protected? At Lukaskrankenhaus, there are a large number of application areas and digital hierarchy levels, all of which serve to accelerate hospital processes. As part of the “Visite 2.0” project, Lukas employees access the patient data via iPad mini and maintain the patient file where the data is created and needed, directly at the patient’s bedside.
This important step on the way to largely paperless hospitals results in numerous advantages. Doctors and nurses always have all the latest diagnostic and care-relevant information, and documentation is simplified and accelerated. This creates a uniform electronic patient record that includes comprehensive documentation of all relevant patient information from admission to the operating theatre and the ward to discharge. With the introduction of Visite 2.0, the possibility of paperless documentation was integrated into the Städtische Kliniken Neuss and thus an important step was taken on the way to a paperless hospital.
Another project concerns telemedicine. All ambulances in Rhein-Kreis Neuss are equipped with telemedical units (Ortivus, Lifenet) that transmit the recordings of the ECGs directly to the Chest Pain Unit of the Lukas Hospital. The significant time gain has led to a 23 percent increase in the number of patients who reach the Lukas Hospital alive after an acute heart attack – a hard-measurable advantage of digitization in healthcare.

